No longer simply a messaging app, Telegram has evolved into a hub for a variety of cybercriminal activities. Its blend of encryption, anonymity, ease of use, and large group and channel features make it an attractive platform for threat actors seeking both privacy and reach. Telegram is now regularly used as a command and control (C2) and data exfiltration channel, with bots also serving as direct pipelines for stolen files and credentials. At the same time, Telegram functions as a thriving marketplace, allowing threat actors to openly advertise compromised databases and credentials, as well as promote hacking services and malware. Notable spikes in Telegram chat activity often also coincide with major geopolitical events, with hacktivist groups using the platform to coordinate campaigns, recruit fellow hackers and spread propaganda. Telegram also lowers the barrier to entry for cybercrime, as while large, organized groups have a more notable presence on the platform, independent hackers and smaller groups can just as easily create their own channels, fueling the rapid growth of Telegram as a legitimate tool that has been hijacked for malicious purposes.
Telegram as a C2 and data exfiltration channel
A growing number of malware families demonstrate how Telegram is increasingly becoming part of threat actors’ toolkits. Instead of building and maintaining their own infrastructure, threat actors are turning to Telegram as a ready-made channel for both C2 communication and data exfiltration.
The malware Raven Stealer, for example, sends stolen data in real-time through Telegram, harvesting credentials, cookies, payment details and browser information with minimal user interaction. Distributed via GitHub and promoted on its Telegram channel ‘ZeroTrace’, it not only uses Telegram as an exfiltration channel but also as a marketing and development hub. Its connections to the malware Octalyn Stealer suggest an evolving portfolio of tools built by the same developers, with Telegram serving as a centralized hub for the promotion of Raven Stealer and other associated malware. Similarly, the CyberEye remote access trojan leverages Telegram to route all C2 traffic via Telegram’s Bot API, eliminating the need for dedicated infrastructure. As a result, the malware is capable of exfiltrating stolen browser credentials, WiFi passwords and Telegram and Discord session data. Likewise, PE32 ransomware is notable for communication entirely via the Telegram Bot API, with victims also instructed to contact attackers via Telegram for ransom negotiations.
Moreover, a recent investigation by Crimson7 researchers into suspicious Telegram activity revealed a large-scale malware campaign built entirely using Telegram’s infrastructure. What first appeared as a phishing attack under the guise of a Google Chrome update, was later revealed to be a sophisticated JavaScript-based infection system capable of exfiltrating victim data in real-time via Telegram’s Bot API. Each successful compromise was reported directly to attacker-run Telegram channels, with more than 18,000 potential victims identified across multiple countries. Beyond exfiltration, Telegram also acted as a file distribution system, hosting hundreds of payloads and stolen data dumps, illustrating how the use of Telegram allows threat actors to lower infrastructure costs and complexity while enabling highly scalable and covert attacks.
Telegram as an online criminal marketplace
Telegram also allows threat actors to openly advertise malware, hacking services, and stolen data. Its blend of public channels and private groups provide both reach and anonymity, creating a convenient marketplace for criminal offerings. Less experienced users can purchase hacking, malware, or ransomware-as-a-service offerings, or hire operators directly through Telegram chats, making malicious and sophisticated services accessible to almost anyone.
Recent research by Open Measures into the Omega Cloud Telegram network highlights the scale of this ecosystem. Launched in 2022, Omega Cloud consists of 11 channels or groups and a single administrator. The network has been used to illegally sell stolen user information logs and has previously used infostealers such as Meta Stealer and RedLine to steal data from victims across multiple countries. Omega Cloud is still active and currently has more than 9,000 subscribers, demonstrating how Telegram networks can operate as self-contained data markets that combine advertising, distribution and sales in one centralized environment. Our own investigation into illicit activity across Telegram linked to ransomware groups like BlackCat revealed how such actors operate large and sophisticated marketplaces, trading stolen credentials and selling them between affiliates and channel members. The scale of these operations is substantial, with multiple alleged corporate breach listings often appearing simultaneously on the BlackCat channel. Data breach announcements on Telegram serve a dual purpose, functioning not only as a commercial tool for facilitating data sales and ransom negotiations, but also as a strategic tool that reinforces the ransomware operation’s reputation as a credible and active threat. Beyond major ransomware groups, smaller channels such as ‘Hackers_of_USA’ offer independent hackers a platform to advertise hacking services and malware and trade stolen data, underscoring the breadth and accessibility of Telegram’s underground economy. By leveraging Silobreaker Chats’ collection, we were able to track these fragmented and fast-moving ecosystems, enabling the identification of emerging threats, common actorsand new breaches in real-time.
Increase in Telegram activity surrounding geopolitical events
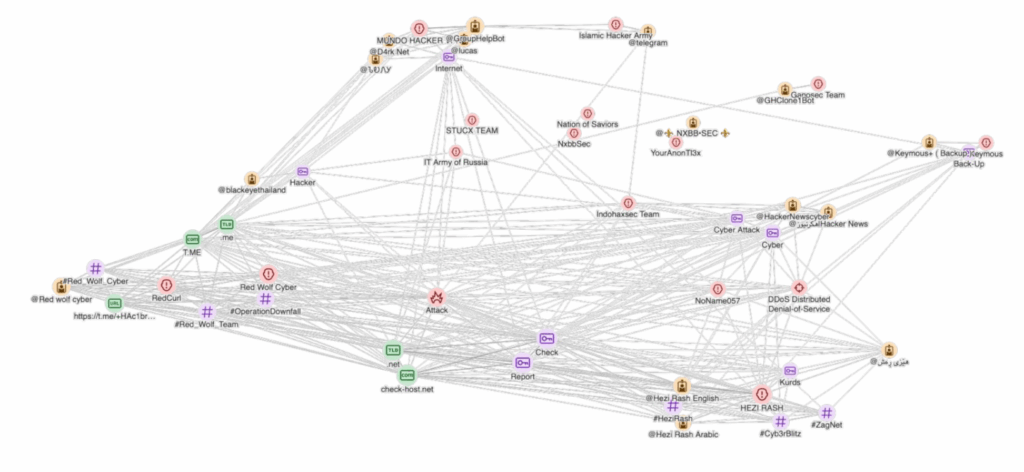
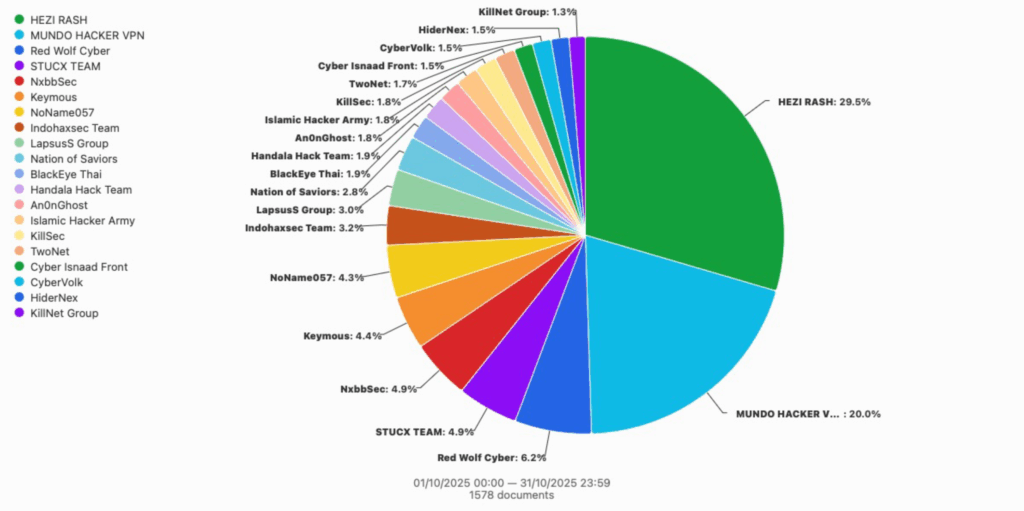
Telegram has become a key platform where hacktivist activity overlaps with real-world geopolitical events. Groups frequently align their operations with ongoing conflicts or political developments, using the platform to coordinate attacks, attract new recruits and frame their actions within broader ideological narratives. This alignment allows Telegram to function not only as a coordination tool, but also as a space where digital operations and geopolitical messaging reinforce one another.
October 2025 and 31. October 2025
Radware researchers observed notable surges in campaigns such as OpIsrael and OpJerusalem, where hashtags including ‘#OpIsrael’, ‘#OpJerusalem’, and ‘#FreePalestine’ signaled coordinated cyber operations targeting Israeli organizations. Between March 18th and March 21st, 2025, the #OpIsrael Telegram channel issued a broad call to action, urging almost 50 hacktivist groups to expand their targeting beyond Israel to include countries perceived as supporting Israeli policies, such as the United States and the United Kingdom. These coordinated appeals encouraged participants to conduct website defacements, data breaches, and distributed denial-of-service attacks, illustrating how Telegram facilitates both operational planning and ideological alignment across dispersed groups.
The alignment between Telegram activity and geopolitical context is further underscored by findings from OpenMinds and DFRLab, who identified a network of 3,634 automated accounts posting pro-Russian comments on Telegram channels between January 2024 and April 2025. The comments included pro-Russian propaganda, anti-Ukrainian propaganda, and anti-war messaging and calls for peaceful coexistence aimed at Ukrainians within Russia-occupied territories. The narratives were often tailored to current events and changes in local conditions.
Our own analysis of Telegram chats further reveals how hacktivist operations often mirror and respond directly to developments in ongoing geopolitical conflicts. Activity observed within the Cyber Toufan Telegram channel demonstrates this alignment, with posts closely tracking events related to the Israel–Hamas conflict. The group’s messaging references ceasefire violations in Gaza, monitoring of Israeli military movements, and criticism of Israeli Prime Minister Benjamin Netanyahu, indicating an ongoing awareness of and reaction to real-world events. Cyber Toufan publicly stated that it would ‘respect the ceasefire’ and suspend operations, while warning that it would retaliate at the ‘first breach of the ceasefire.’ Subsequent posts reinforced this intent, announcing claimed breaches and the hacking of 17 institutions and companies that ‘directly and indirectly serve the Zionist defense and military industries.’ The group claimed to be in possession of personal data, administrative and technical documents, audio calls, and video recordings, framing the operation as a direct response to alleged ceasefire violations and the ‘spilling of our brothers’ blood.’
This sequence of posts illustrates how Telegram functions as a platform where cyber operations, political messaging and real-world conflict dynamics converge. Through Telegram chat monitoring, these narratives can be tracked and contextualized in real-time, allowing analysts to connect cyber campaigns with corresponding geopolitical triggers and to better understand the motivations underpinning coordinated hacktivist activity.
Telegram’s transformation from a messaging app into a tool cybercrime reflects a broader shift in how threat actors exploit legitimate digital platforms. Its accessibility, anonymity, and ease of use have been leveraged by a wide spectrum of malicious actors, ranging from organized ransomware groups and malware developers to independent hackers and hacktivists. Its use as both a C2 and a data exfiltration mechanism for certain malware strains further enables attackers to streamline communication, conceal infrastructure and automate the theft and distribution of stolen data. At the same time, Telegram’s role in geopolitical conflicts highlights how digital and ideological fronts increasingly overlap, as threat actors leverage the platform not only for attack coordination but also for influence and propaganda. Ultimately, as threat actors continue to innovate and adapt their tactics around Telegram’s infrastructure, organizations must strengthen their threat intelligence capabilities to detect and contextualize emerging risks.
If you want to learn more about how Silobreaker’s deep and dark web offering can help you monitor malware developments and data leaks in underground chats, or connect the dots between geopolitical events and cyberattacks, get in touch here.