With millions of phishing attacks targeting businesses daily, the potential consequences include financial loss, disruption, brand damage, and customer impact. It’s now more critical than ever for organizations to gain clear visibility into the risks they face and be equipped with the relevant intelligence to safeguard their operations.

Detect phishing attacks targeting your business
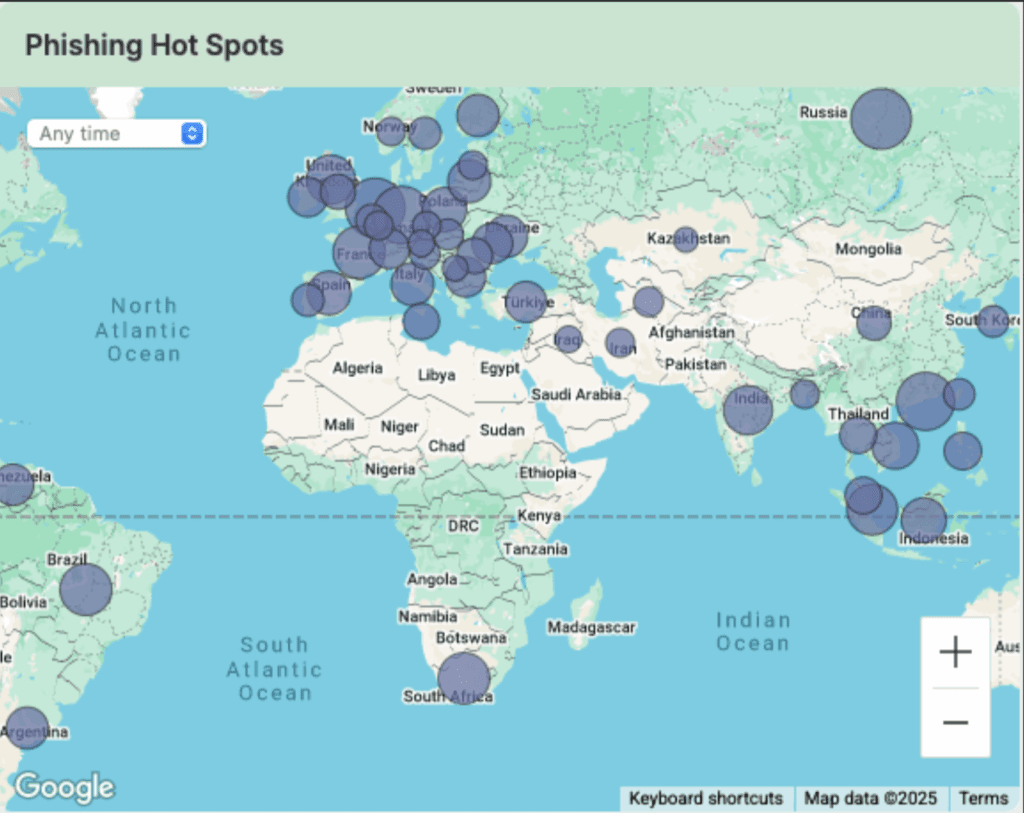
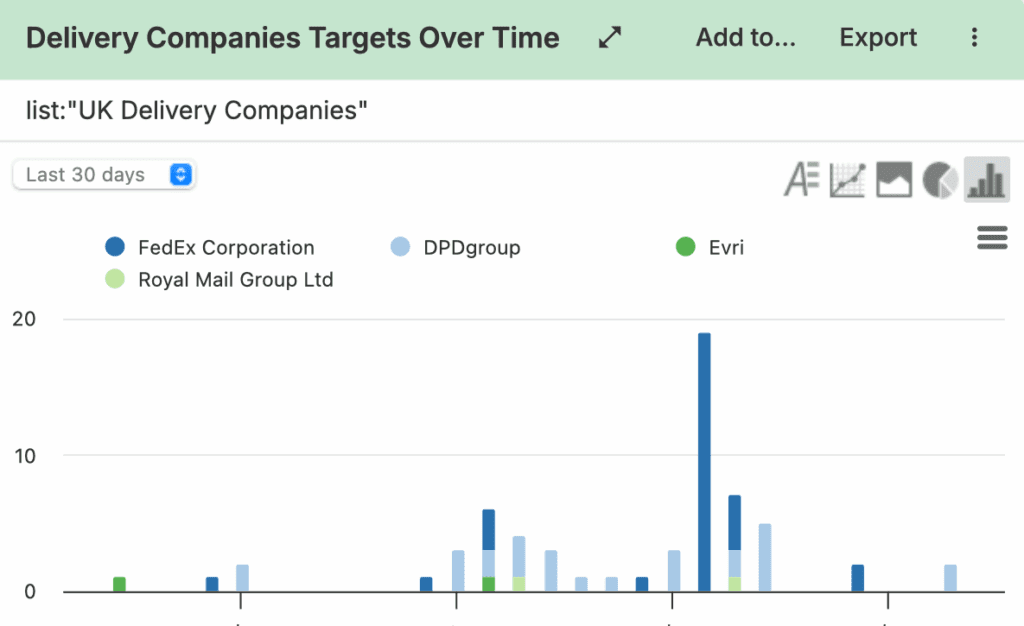
Stay on top of ongoing phishing campaigns targeting your organization, employees or customers through the analysis of trends and tactics used by threat actors. By aggregating real-time data from research blogs, feeds and finished intelligence your team will gain comprehensive insights into the emerging trends that could pose a threat to your business.
Take action against phishing attacks
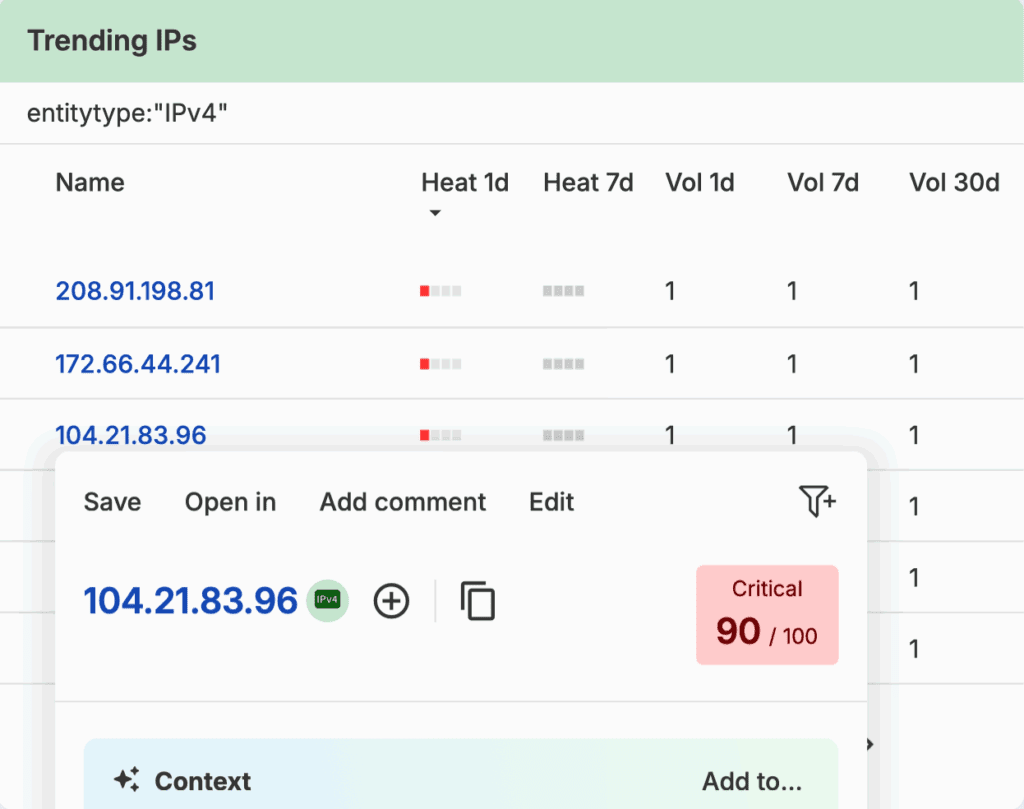
Build automated alerts based on customized watchlists for brands, domains, and credentials. Monitor who is being targeted, which compromises have occurred, and which common tactics are being used in phishing attacks. Armed with this intelligence, your stakeholders can take decisive action to implement proactive measures against potential threats.
Capabilities
Unrivalled visibility into phishing trends, including targets and IOCs, drawn from millions of OSINT and dark web sources
Unified view of targeted industries, brands, domains, IP addresses and vulnerabilities exploited in phishing campaigns
AI-powered automated report building with customizable alerts for key stakeholders
Find your phishing risks today
See how Silobreaker can help your organization monitor ongoing phishing campaigns.