Unpatched vulnerabilities are associated with nearly 60% of breaches and the mean time to exploitation has dropped to only 44 days. For defenders and vulnerability management teams the patching challenge may appear insurmountable. But the reality paints a different picture: less than 1% of all disclosed vulnerabilities are classified as “highest risk”, where severity status and active exploitation demand the fastest possible remediation. So prioritization is key.
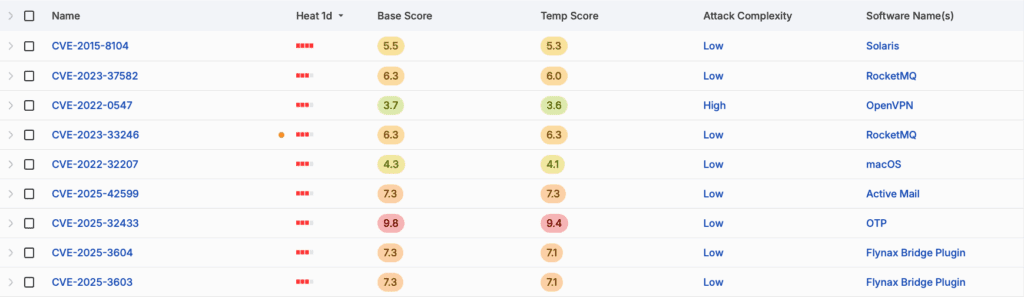
Identify your most critical and exploited vulnerabilities
Understand which vulnerabilities are being actively exploited in the wild, which have proof-of-concept exploits and which ones pose the highest risk to your organization, based on threat actor interest, scoring and industry. Comprehensive coverage ensures you get the full picture.
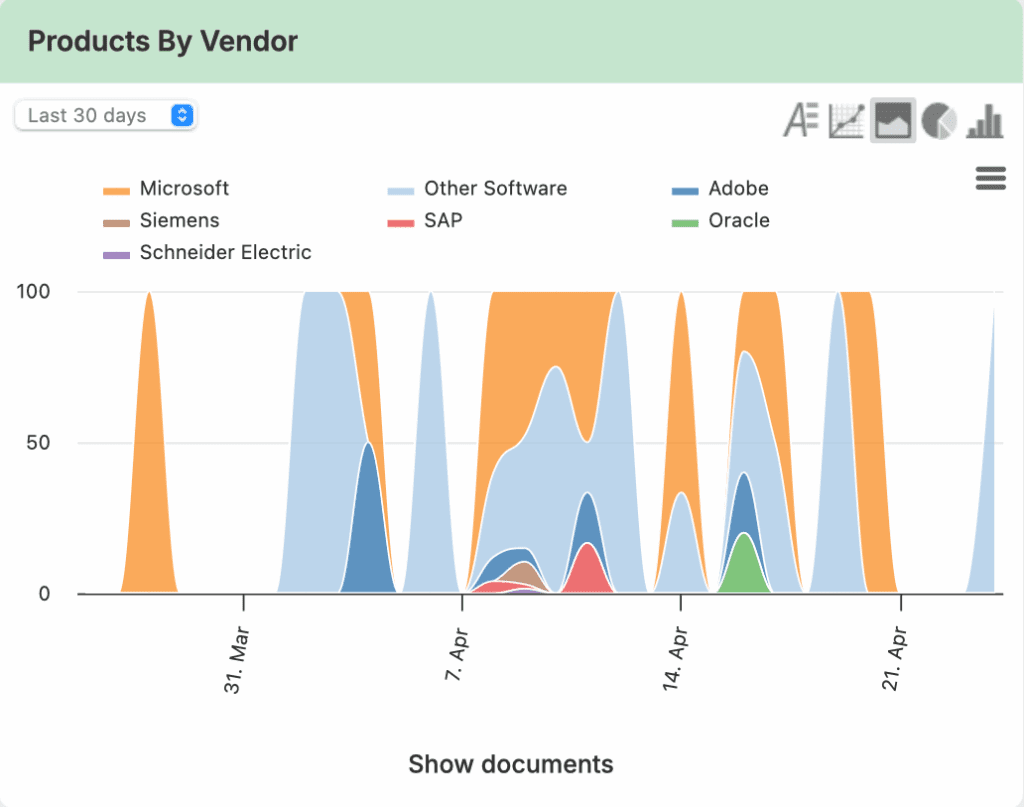
Use intelligence to prioritize patching
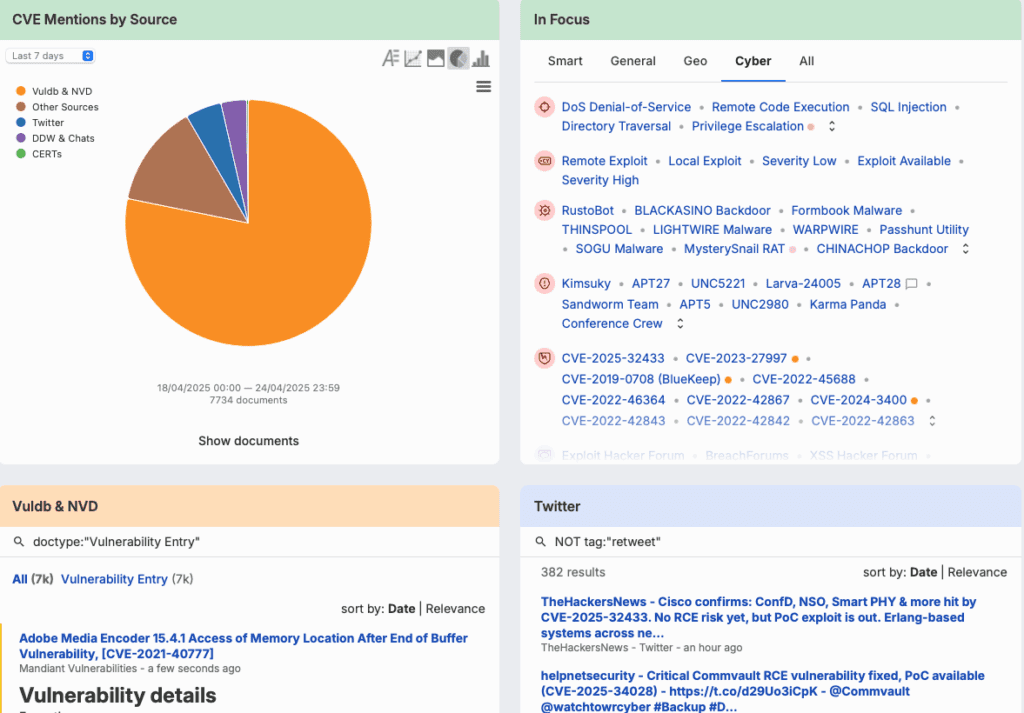
Combine timely and comprehensive vulnerability data with the activities and discussions of threat actors, security researchers and other experts. Access everything you need in one place, and seamlessly pivot from finished intelligence to raw chatter.
Capabilities
Expansive coverage of open, deep, dark, structured and finished intelligence sources
Centralized visibility into actors, malware and emerging threats
High-speed vulnerability notifications and alerting
CVSS3, EPSS and CTI trend scoring for CVEs
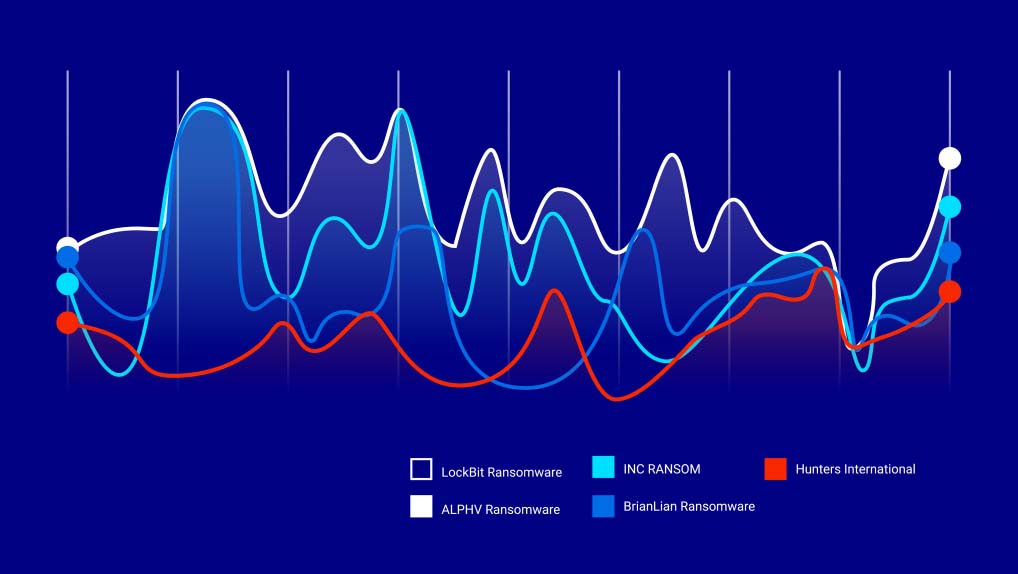
Ransomware and industry dashboards
Finished intelligence and daily briefs on vulnerability exploitation
Find and prioritize the vulnerabilities that matter. Faster
Uncover your top vulnerabilities and understand their priority to your organization with a Silobreaker demo today.