What is the threat intelligence lifecycle?
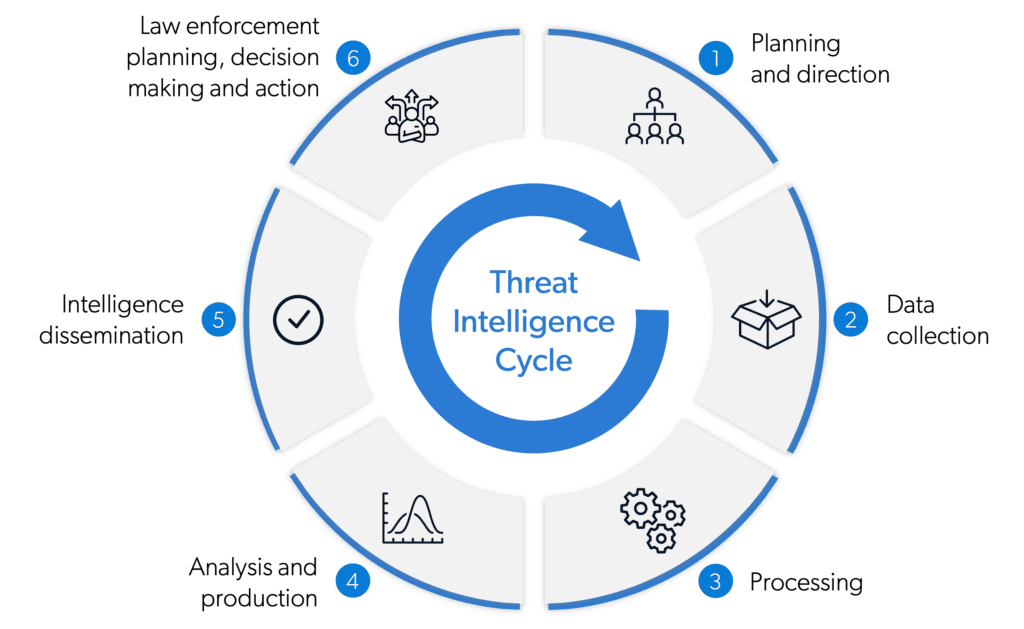
The threat intelligence lifecycle is a step-by-step framework that helps organizations manage and use threat intelligence effectively. It ensures that information about potential threats is handled carefully, and provides a guide that organizations can follow to stay informed about potential risks and protect against them. This security intelligence lifecycle enables organizations to gather data on threats with confidence, analyze it for accuracy and reliability, and take action to protect themselves.
By following this process, intelligence teams can build an efficient threat intelligence process.
The six steps in the intelligence lifecycle include:
- Planning and direction
- Data collection
- Processing
- Analysis and production
- Intelligence dissemination
- Feedback and improvement
The phases of the threat intelligence lifecycle, explained
1. Planning and direction
The threat intelligence lifecycle begins with planning. At this stage, an organization defines their threat intelligence program’s goals, scope and requirements, including their risk tolerance, intelligence needs and the key assets to protect. Factors to consider include their industry, the threat landscape and the specific risks they face.
2. Data collection
In the second stage, a variety of sources are consulted in order to draw relevant information about potential threats. These sources can include open, deep and dark web sources, as well as intelligence platforms that aggregate threat data from multiple sources. Manual research, automated tools or a combination of both are used to collect data, which organizations can then use to better understand the current threat landscape.
3. Processing and analysis
After data is collected, the next phase is processing, validating and analyzing the data to extract actionable intelligence. This involves examining and contextualizing it to identify patterns, trends and potential threats. Deeper analysis is carried out using a variety of analytical techniques, such as data mining for patterns, relationships and insights, machine learning and human expertise.
4. Production
The fourth stage of the threat intelligence cycle is production. The analyzed intelligence is transformed into consumable formats such as reports, alerts or tactical advisories, and tailored to the specific needs of various stakeholders, including security teams and incident response teams.
5. Intelligence dissemination
After it has been analyzed and tailored to suit their needs, the threat intelligence is shared with relevant stakeholders to support decision-making and proactive defense measures. Delivering intelligence on time ensures that it is received by the right individuals or systems so that appropriate action can be taken. Dissemination can be carried out through emails, security dashboards, or other communication channels.
6. Feedback and improvement
In the final phase, ongoing feedback is gathered from stakeholders to assess the effectiveness and relevance of the threat intelligence lifecycle. The six phases form a cyclical process, where feedback from this stage guides the planning and direction for future iterations of the threat intelligence lifecycle.
The threat intelligence lifecycle is a continuous process that involves turning structured and unstructured data into relevant information for organizations so they can stay ahead of threats, identify vulnerabilities and take proactive measures to detect and protect their systems and assets from emerging threats – reducing their overall risk exposure.
How can you optimize your threat intelligence lifecycle?
Silobreaker was built with the traditional security intelligence cycle in mind. It simplifies the selection and coordination of priority intelligence requirements (PIRs) and streamlines the time-consuming selection and collection of open, deep and dark web sources, as well as premium and custom sources of intelligence.
Make sense of unstructured data at scale, and produce and share high-quality intelligence at pace. With our platform, you can analyze and process complex data, generate relevant reports, and seamlessly communicate with multiple stakeholders, all in a single workflow.
Find out how Silobreaker can deliver dramatic efficiency gains, while helping you to meet your PIRs, reduce risk and response times, and provide decision-makers with actionable intelligence faster.